An effective information security analyst resume requires showcasing a blend of technical expertise, problem-solving skills, and a commitment to safeguarding sensitive data.
In this guide, we will walk you through the essential steps to create a resume that will get you hired in no time. From picking the right structure to detailing your accomplishments, we'll provide practical tips and examples to help you stand out to potential employers.
Whether you're a recent graduate college student or a specialist with experience, we have all you need to craft a winning resume.
Information security resume examples
- Senior information security analyst resume
- Chief information security officer resume
- Entry-level IT security analyst resume
- Network security analyst resume
- Malware information security analyst resume
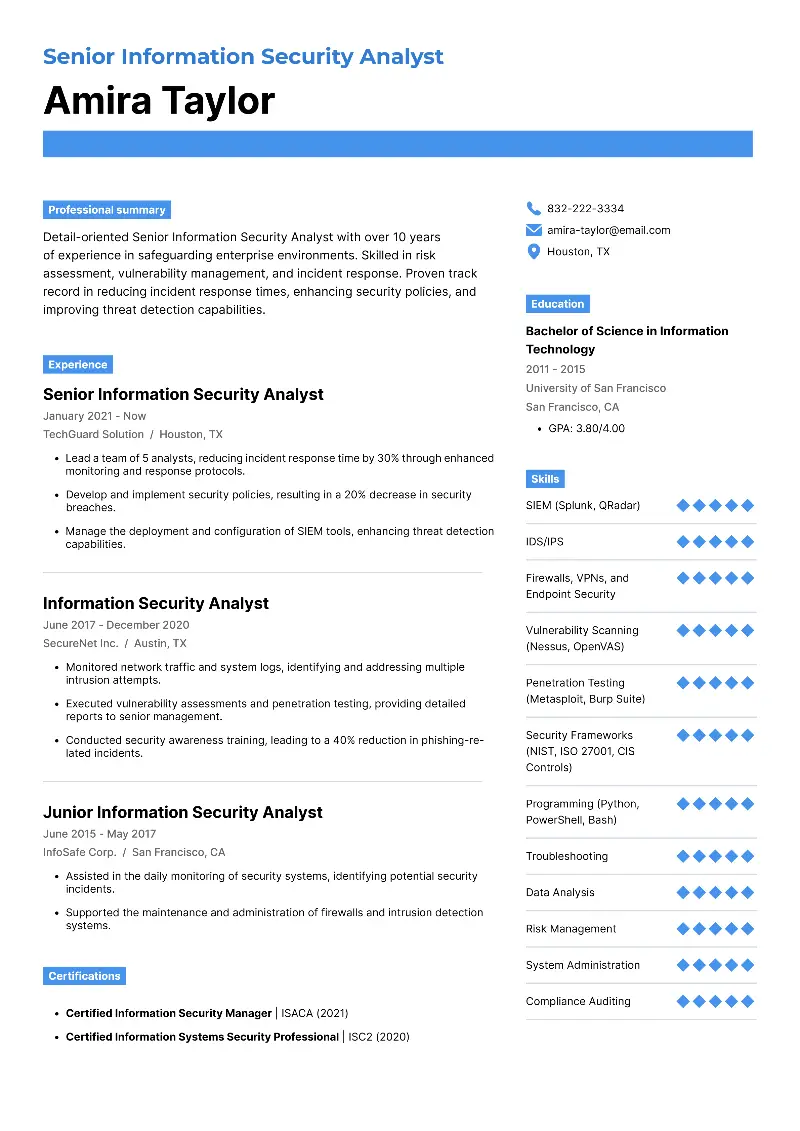
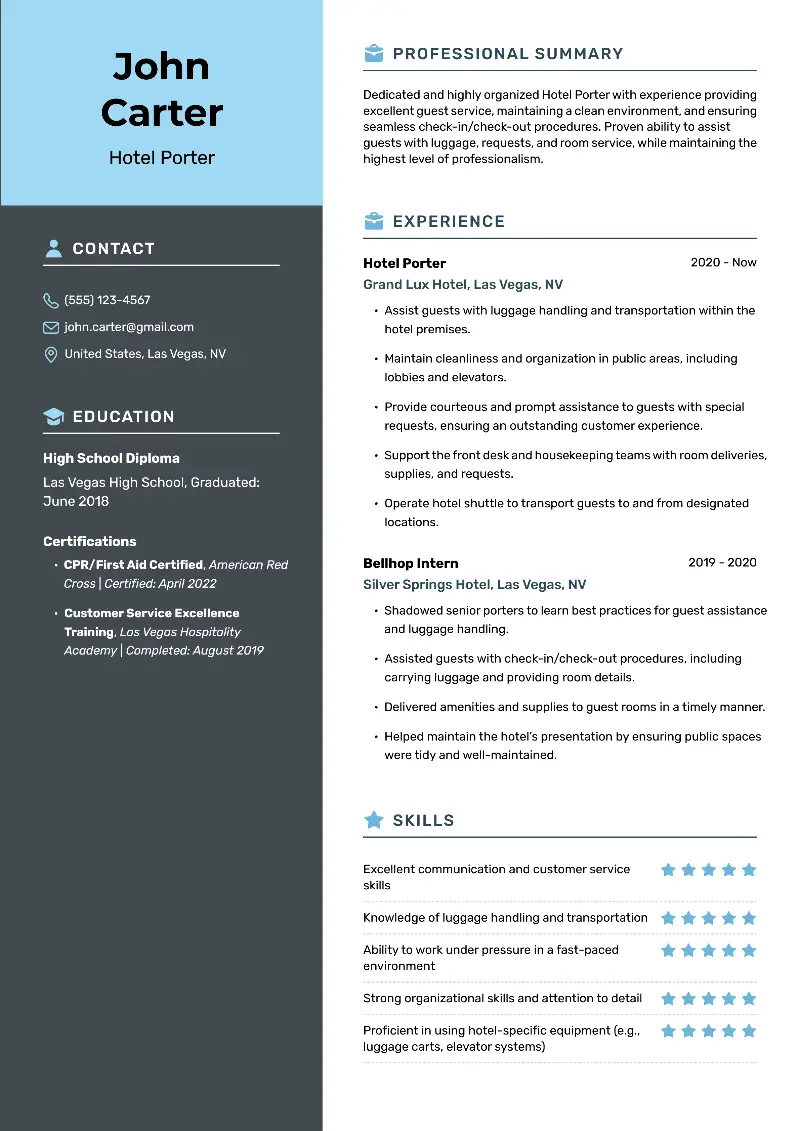
Senior information security analyst resume example
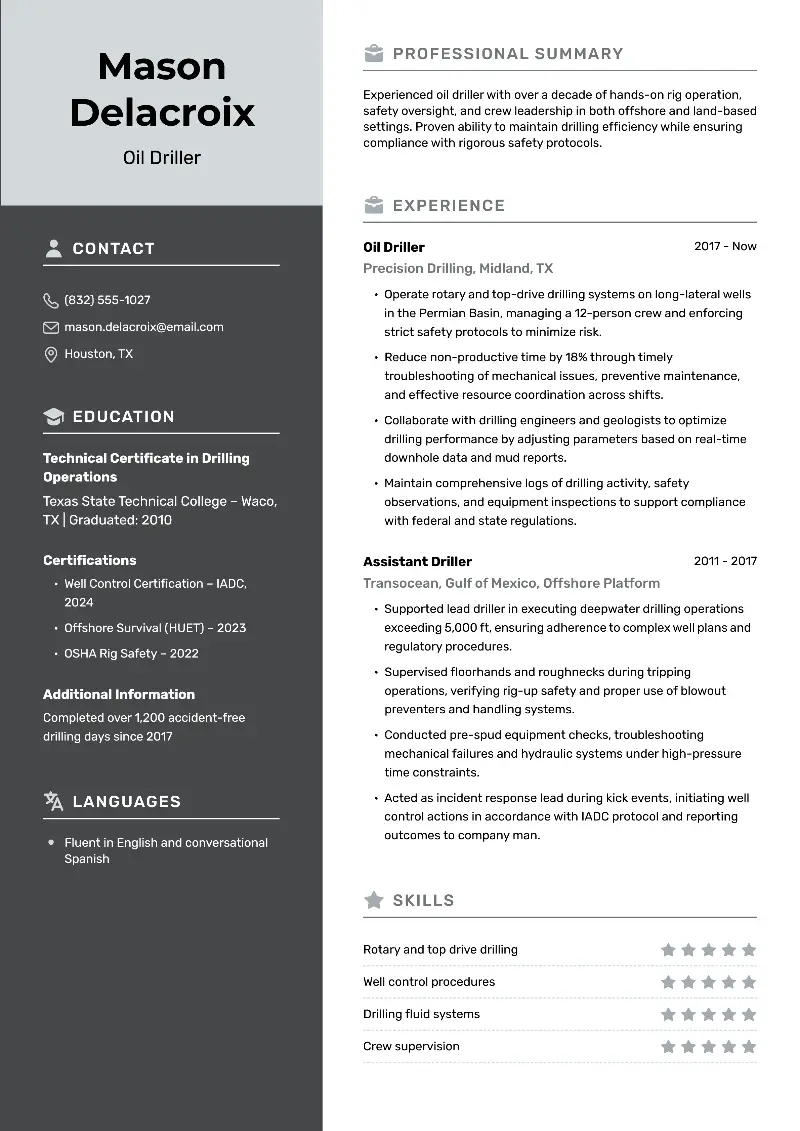
Chief information security officer resume example
Marcus Reeves
marcus-reeves@email.com | 832-222-3334 | New York, NYProfessional Summary
Seasoned Chief Information Security Officer with extensive experience in leading and developing robust cybersecurity strategies for global enterprises. Expertise in risk management, regulatory compliance, and incident response. Proven ability to align security initiatives with business objectives, reduce risk, and ensure the protection of critical assets.
Professional Experience
Chief Information Security Officer (CISO) | GlobalTech Solutions (New York, NY)
January 2019 – Present
- Direct a global cybersecurity strategy, reducing security incidents by 40% through enhanced threat detection and response mechanisms.
- Establish a comprehensive risk management framework, aligning security practices with business goals and regulatory requirements.
- Lead a team of 25 security professionals, fostering a culture of continuous improvement and innovation in cybersecurity practices.
Vice President of Information Security | SecureWorld Corp. (San Francisco, CA)
June 2014 – December 2018
- Developed and implemented an enterprise-wide security program, resulting in a 30% reduction in vulnerabilities and compliance gaps.
- Oversaw incident response operations, effectively managing and mitigating the impact of significant security breaches.
- Collaborated with executive leadership to integrate cybersecurity into the company’s strategic planning and operations.
Director of Information Security | CyberNet Solutions (Austin, TX)
March 2010 – May 2014
- Managed the implementation of security policies and procedures, achieving ISO 27001 certification for the organization.
- Led a successful overhaul of the company's security infrastructure, enhancing protection against advanced threats.
- Conducted regular security audits and risk assessments, providing actionable recommendations to senior management.
Senior Information Security Analyst | CyberNet Solutions (Austin, TX)
July 2006 – February 2010
- Performed in-depth analysis of security incidents, reducing response times by 25% through improved monitoring and detection systems.
- Assisted in the development of security awareness training programs, increasing employee compliance with security policies.
- Conducted vulnerability assessments and penetration tests, identifying and mitigating critical security risks.
Education
Master of Science in Information Security | Stanford University
- Graduated: May 2006
- GPA: 4.0/4.0
Bachelor of Science in Computer Science | University of California, Berkeley
- Graduated: May 2002
- GPA: 3.9/4.0
Certifications
- Certified Chief Information Security Officer (CCISO) | 2019
- Certified Information Systems Auditor (CISA) | 2015
- Certified Information Security Manager (CISM) | 2012
- Certified Information Systems Security Professional (CISSP) | 2008
Skills
- Leadership & Management: strategic planning, team leadership, project management
- Technical Skills: SIEM (Splunk, ArcSight), IDS/IPS, firewalls, VPNs, endpoint security, cloud security (AWS, Azure)
- Risk & Compliance: risk management, regulatory compliance (GDPR, HIPAA, PCI-DSS), incident response, security audits
- Soft Skills: strong analytical skills, excellent communication, problem-solving, attention to detail
Professional Affiliations
- Member, Chief Information Security Officer (CISO) Network
- Member, SANS Institute
- Member, International Information System Security Certification Consortium (ISC)²
- Member, Information Systems Security Association (ISSA)
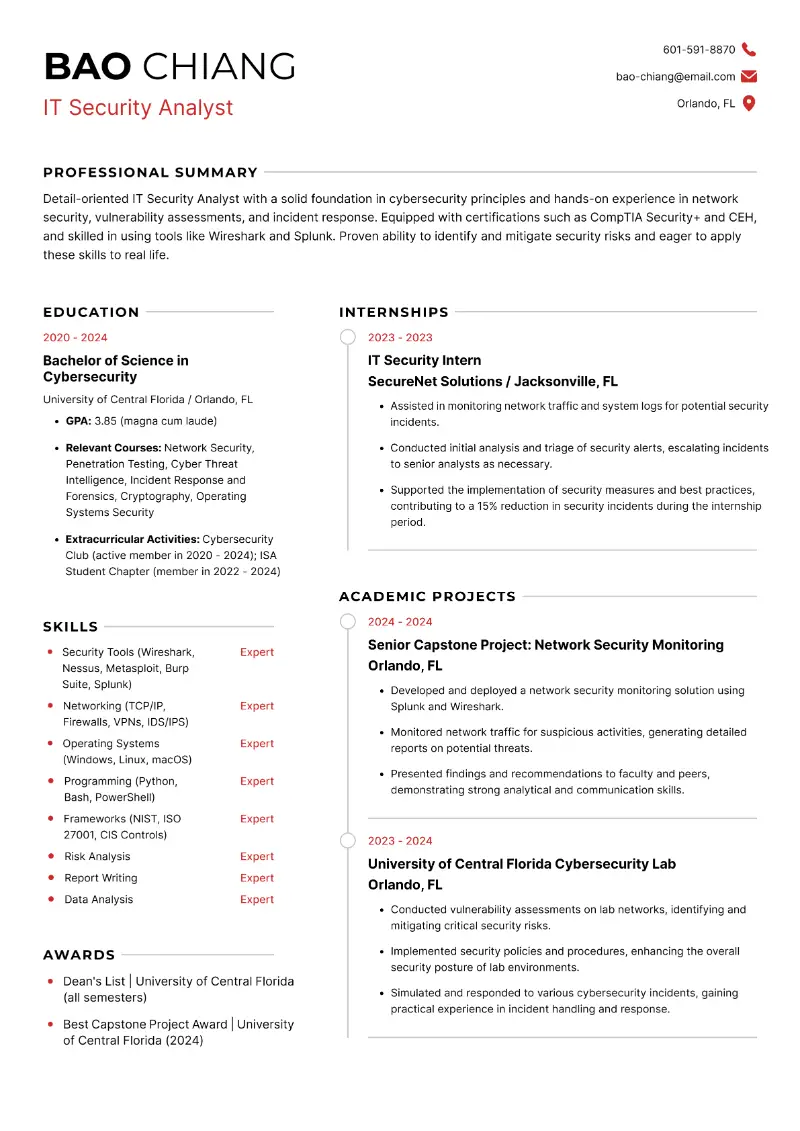
Entry-level IT security analyst resume example
Network security analyst resume sample
Professional Summary
Highly skilled and dedicated Network Security Analyst with experience in protecting organizational assets from cyber threats. Proficient in implementing security measures, conducting risk assessments, and ensuring compliance with industry standards. Adept at utilizing cutting-edge technologies and methodologies to safeguard network integrity, confidentiality, and availability.
Professional Experience
Network Security Analyst
Caterpillar Inc., Peoria, IL, March 2018 – Present
- Implement and manage network security systems, including firewalls, IDS/IPS, and VPNs, ensuring robust protection against cyber threats.
- Analyze security breaches and incidents, leading investigations and implementing corrective actions to prevent recurrence.
- Manage and monitor SIEM solutions to detect and respond to security events in real-time.
- Conduct penetration testing to evaluate the effectiveness of security measures and identify areas for improvement.
- Provide security training and awareness programs for employees to promote a culture of security within the organization.
Information Security Specialist
State Farm, Bloomington, IL, June 2014 – February 2018
- Designed and implemented network security solutions to protect company data and systems from unauthorized access and cyber-attacks.
- Performed regular risk assessments and security audits, developing remediation plans for identified vulnerabilities.
- Monitored network traffic for suspicious activity, employing intrusion detection and prevention systems to safeguard the network.
- Developed and maintained security policies, standards, and guidelines in alignment with industry best practices and regulatory requirements.
- Assisted in incident response efforts, including forensic analysis, documentation, and reporting of security incidents.
Junior Network Security Analyst
John Deere, Moline, IL, May 2012 – May 2014
- Supported senior analysts in the implementation and management of network security tools and technologies.
- Conducted basic vulnerability assessments and security audits, reporting findings to senior team members.
- Assisted in the configuration and maintenance of firewalls, IDS/IPS, and other security infrastructure components.
- Monitored security logs and alerts, escalating potential threats to senior analysts for further investigation.
Education
Bachelor of Science in Information Technology
Southern Illinois University, Carbondale, IL
- Graduated: May 2011
Technical Proficiencies
- Network Security Tools: Wireshark, Nessus, Snort, Metasploit
- Firewalls: Palo Alto, Cisco ASA, Fortinet
- SIEM: Splunk, IBM QRadar, ArcSight
- Operating Systems: Windows, Linux, UNIX
- Programming/Scripting: Python, Bash, PowerShell
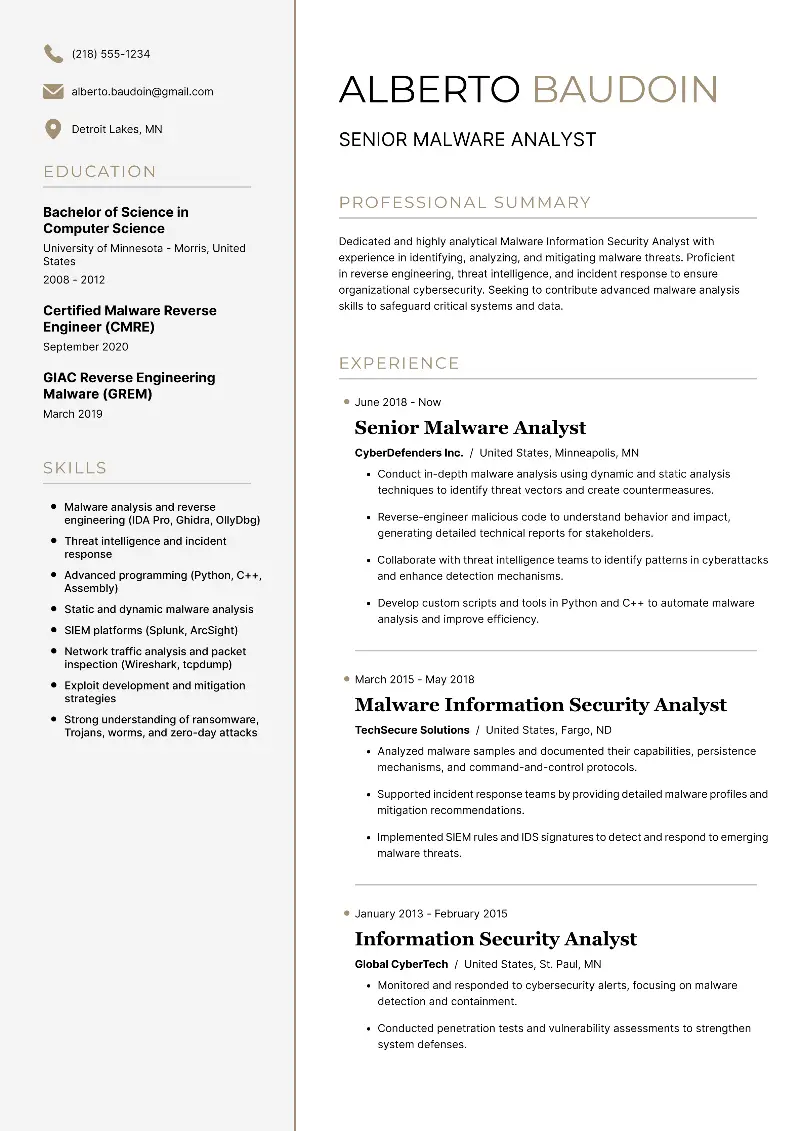
Malware information security analyst resume template
Information security vs cybersecurity
While there is some overlap in their responsibilities, an information security analyst and a cybersecurity analyst are not necessarily the same job.
Information security analysts typically focus on protecting an organization's data, systems, and networks from breaches and unauthorized access.
On the other hand, cybersecurity analysts specialize in detecting, analyzing, and responding to cyber threats, including identifying vulnerabilities and mitigating risks in the digital environment.
| Aspect | Information Security Analyst | Cybersecurity Analyst |
|---|---|---|
| Responsibilities | Implementing security measures, policies, and protocols. | Recognizing weaknesses and minimizing potential threats. |
| Scope | Broad focus on data protection and compliance. | Specialized in threat detection and response. |
| Tasks | Conducting risk assessments, audits, and security reviews. | Monitoring security systems and analyzing incidents. |
| Skills | Proficiency in security tools, risk assessment, and compliance. | Strong analytical skills, threat intelligence, and incident response. |
| Collaboration | Collaborates with teams to enforce security measures. | Works closely with IT and security teams for threat mitigation. |
| Certifications | CISSP, CISM, CISA, CompTIA Security+. | CEH, CISSP, CISA, CompTIA Cybersecurity Analyst. |
While the two specialists share common work goals of enhancing security, their roles differ in emphasis and scope within an organization's cybersecurity framework.
Contact information
This section is one of the most straightforward yet crucial parts of your resume. As an information security analyst, presenting your contact details clearly and professionally is essential for making a good first impression.
What you need to include in contact resume section:
- Full Name. Write your full legal name. If you have a very common name, consider including your middle name initial to differentiate yourself.
- Phone Number. State a reliable phone number where you can be reached during business hours. Ensure your voicemail greeting is appropriate for HR to hear.
- Email Address. Provide an email address that has your name. Avoid using nicknames or non-professional email domains.
- LinkedIn Profile. Share a link to your LinkedIn page as it can give potential employers more insight into your background.
- Physical Address. While your full address is not necessary, you may want to at least add your city and state.
- Portfolio or Website (if applicable). If you have a professional website or online portfolio that showcases your work, write the URL.
- Alternative Contact Methods. Consider adding a secondary email or phone number if you want to ensure uninterrupted communication.
In case you prefer working online, specify it on your information security analyst resume by writing "remote" in the location field.
Resume summary and objective
You can choose where you want your information security analyst resume to begin with a summary or an objective. Each serves a different purpose and should be tailored to your career stage and goals.
Resume Summary
A resume summary is a concise overview of your professional achievements, skills, and experience. It's ideal for candidates with several years of experience in the field. The summary should provide a snapshot of your career and convey your value to potential employers.
Resume summary writing tips:
- Be Concise. Limit your summary to 3-4 sentences.
- Highlight Key Achievements. Focus on your most significant accomplishments and skills.
- Use Keywords. Incorporate relevant keywords from the job description to pass through applicant tracking systems (ATS).
- Tailor to the Job. Customize your summary for each position you apply for, emphasizing the most relevant experience and skills.
Detail-oriented IT Security Analyst with over 5 years of experience in safeguarding enterprise environments. Proven expertise in risk assessment, vulnerability management, and incident response. Successfully reduced security incidents by 30% at TechGuard Solutions through proactive monitoring and threat intelligence. Certified CISSP and CEH, committed to maintaining the highest standards of information security.
Resume Objective
A resume objective is a brief statement that outlines your professional goals and explains why you are interested in a specific position. It's particularly useful for entry-level candidates or those transitioning into a new field. The objective should reflect your aspirations and how they align with the company’s needs.
Resume objective writing tips:
- Be Specific. Clearly state your career goals and how they relate to the job you’re applying for.
- Show Enthusiasm. Convey your passion for the role and the company.
- Keep it Short. Limit your objective to 2-3 sentences.
- Focus on Value. Highlight how your background and skills will benefit the employer.
Motivated and detail-oriented cybersecurity graduate seeking an entry-level IT Security Analyst position. Eager to apply hands-on experience in network security and incident response gained through internships and academic projects. Committed to contributing to the protection of organizational data and systems.
Choosing the right option depends on your experience level and goals, but both can effectively showcase your qualifications and set the tone for the rest of your information security analyst resume.
Work experience
The experience segment in your resume is your main selling point. To effectively organize this part of your information security analyst resume, list your employment history chronologically, starting with your most recent position.
Clearly state the job title you held and the dates you worked in that position. Include the name of the company or organization where you worked and its location.
Under each role, list your main responsibilities and achievements. Where possible, quantify your accomplishments with numbers or percentages. It's also advisable to mention any specific software or tool you used in each role.
Example of work experience on a resume:
Information Security Analyst
SecureTech Solutions (New York, NY)
January 2020 - Present
- Conduct regular security assessments and vulnerability scans, resulting in a 25% decrease in identified risks.
- Develop and implement security policies and procedures in compliance with industry regulations such as GDPR and HIPAA.
- Lead incident response efforts, investigating and mitigating security breaches to minimize the impact on company operations.
Security Operations Analyst
CyberGuard Inc. (New York, NY)
June 2017 - December 2019
- Monitored and analyzed security events using SIEM tools, identifying and responding to potential threats in real time.
- Collaborated with cross-functional teams to design and implement controls, enhancing the company's overall security posture.
- Provided technical expertise and support during security incidents, ensuring timely resolution and minimal disruption to business operations.
Education
Including your academic history in a information security analyst resume is integral for demonstrating your theoretical foundation. Here, you need to provide recruiters with a clear understanding of your educational background in information security.
For each education entry, list the following details:
- Specify the type of degree you obtained and the major you had.
- Mention the name of the university or college where you earned your credentials.
- Include the city and state where the institution is located.
- Provide the details on when you attended the school, including both the start and end dates or the expected graduation date.
- Indicate participation in extracurricular activities or clubs related to your field of study.
You can also add specific coursework you've completed (especially relevant to entry-level candidates) and academic honors or awards you've received to strengthen your application.
Organize this section in reverse chronological order, starting with the most recent credentials received.
Example of education on resume:
Master of Science in Cybersecurity | Northeastern University (Boston, MA)
- Graduated in May 2023
- Specialization: Network Security
- Thesis: "Advanced Techniques in Intrusion Detection Systems"
- GPA: 3.90/4.00
Bachelor of Science in Computer Science | Emerson College (Boston, MA)
- Graduated in May 2020
- Minor: Information Security
- Relevant Coursework: Cryptography, Network Security, Secure Software Development
- Senior Project: "Design and Implementation of a Secure Authentication System"
- GPA: 3.80/4.00
When organizing your academic information, be concise and specific. Additionally, verify that all the information is accurate so employers can check it.
Certifications
For information security analysts, certifications help prove your professional expertise. The following certificates are often required or preferred:
- Certified Information Systems Security Professional (CISSP): The gold standard for IT professionals. It requires five years of work experience and a deep understanding of various aspects of information security.
- Certified Ethical Hacker (CEH): This certification allows you to indicate your comprehension of standard hacking techniques and methods for identifying and mitigating potential threats.
- Certified Information Security Manager (CISM): Demonstrate mastery in organizational concerns, risk management, and systems audit.
- GIAC Security Essentials Certification (GSEC): Confirmation of your familiarity with fundamentals such as authentication, cryptography, and others.
- CompTIA Security+: Validates your knowledge of basic safety concepts, principles, and practices.
- Certified Cybersecurity Analyst (CySA+): Focuses on threat detection and incident response within cybersecurity environments.
These credentials will help you protrude among other applicants by manifesting your commitment to the field.
Information security analyst's skills
For IT specialists, this part is sometimes more important than the school they graduated from or the number of years of experience. Hence, spend time detailing the skillset you have to offer.
Hard skills are job-specific abilities that are developed through professional practice.
Examples of hard skills:
- Network security
- Penetration testing
- Firewall configuration
- Risk assessment
- Incident response
- Security information and event management (SIEM)
- Cryptography
- Intrusion detection systems (IDS/IPS)
- Vulnerability assessment
- Security policy development
- Compliance management
- Data loss prevention (DLP)
- Security assessment tools (e.g., Nmap, Metasploit)
- Security incident handling procedures
- Identity and access management (IAM)
- Endpoint protection strategies and implementation
- Cloud security architecture and controls
- Malware analysis and reverse engineering
Soft skills are transferable and can be applied to a variety of jobs.
Examples of soft skills:
- Communication
- Problem-solving
- Critical thinking
- Attention to detail
- Analytical thinking
- Adaptability
- Teamwork
- Time management
- Creativity
- Ethical judgment
- Conflict resolution
- Stress management
- Emotional intelligence
Brainstorm what skills you have developed throughout your college education or previous work to better present your professional expertise.
Additional sections
You can include any information your proposed employer should know about you in your information security analyst resume. See some examples of supplementary sections below.
| Section | Description |
|---|---|
| Projects or Research | Highlighting significant projects, research papers, or case studies undertaken, demonstrating practical experience and problem-solving abilities. |
| Publications or Presentations | Listing authored publications, whitepapers, or presentations delivered at cybersecurity-related events or conferences, showcasing thought leadership and expertise. |
| Internships | Describing previous internships or relevant work experiences gained during academic studies or early career, demonstrating practical skills and knowledge. |
| Professional Affiliations | Mentioning memberships in cybersecurity-related professional organizations or associations, indicating a commitment to staying updated with industry trends and networking. |
| Recommendations | Providing contact information for professional references who can vouch for skills and character. |
| Awards | Noting any recognition or accolades received for outstanding performance, achievements, or contributions in the field of information security. |
| Languages | Indicating proficiency in multiple languages, especially those relevant to the industry or work environment. |
| Hobbies | Sharing personal interests that highlight well-roundedness or elaborate on your teamwork, problem-solving, or analytical skills. |
Including these additional sections can provide a more comprehensive picture of your qualifications, experiences, and interests as an information security analyst.
Use a resume builder
Tired of staring at a blank page, wondering where to begin with your information security analyst resume? There's an ultimate solution for crafting a professional document with ease - Resume Trick!
With a user-friendly interface and customizable and printable resume templates, this builder streamlines the writing process, saving you time and frustration.
Benefits:
- Professional Layouts. Access a variety of sleek and modern templates designed by professionals to make your resume stand out.
- Quick Editing. Easily make updates and revisions to your information security analyst resume, saving valuable time and effort.
- AI Assistance. Receive helpful suggestions from AI-powered tools to optimize your professional summary and work experience sections, helping to catch the attention of recruiters.
Don't let the daunting task of writing hold you back. Harness the power of the online resume builder and take the next step in your career today!
Create your professional Resume in 10 minutes for FREE
Build My Resume
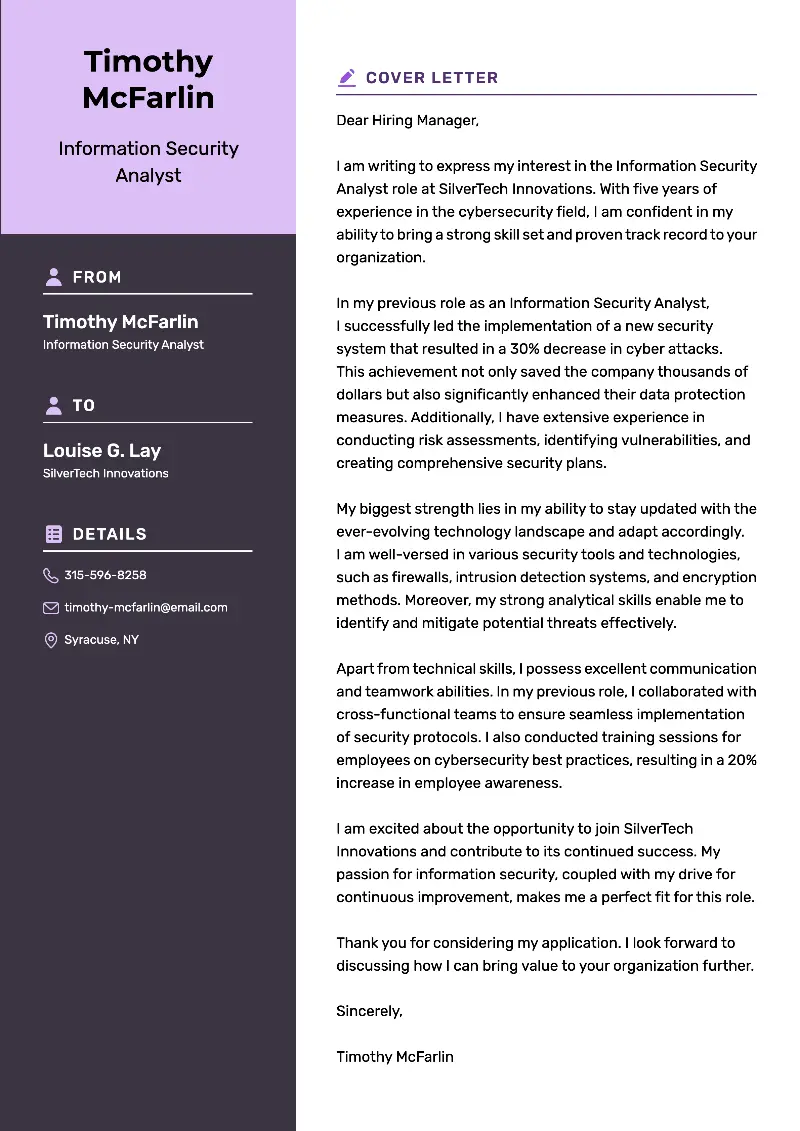
Information security analyst cover letter
A good cover letter is essential for landing an information security analyst job. It is your chance to show employers why they should hire you.
Tips on how to compose an outstanding supporting letter:
- Be concise and professional. Keep your cover letter brief and to the point, focusing on the most relevant information and maintaining a professional tone throughout.
- Address the hiring manager. Whenever possible, address the cover letter to the hiring manager by name for a personal touch.
- Tailor to the job description. Highlight your relevant skills and experiences that match the requirements listed in the job description.
- Showcase your passion. Demonstrate your enthusiasm for the field of information security and your commitment to staying updated with the latest trends and technologies.
- Express your Interest in the company. Explain why you're interested in working for the specific company and how your skills and experience align with their mission and values.
- Highlight your achievements. Discuss any notable achievements or projects that you've worked on, especially those that demonstrate your ability to solve complex issues.
- Provide specific examples. Use concrete examples from your previous work experience to showcase your expertise in areas such as risk assessment or security policy development.
- End with a call to action. Conclude your information security analyst cover letter with a strong closing statement expressing your desire to further discuss how you can contribute to the company's success.
Good information security analyst cover letter example:
Dear Ms. Muriel Sluder,
I am writing to express my interest in the information security analyst position at CyberDefense Solutions, as advertised on your company's career page. With a strong background in cybersecurity and a passion for protecting sensitive information, I am confident in my ability to contribute effectively to your team.
In my previous role at SecureTech Innovations, I was responsible for conducting regular security assessments and implementing proactive measures to mitigate potential risks. I have experience in analyzing security incidents, identifying vulnerabilities, and developing comprehensive strategies to enhance overall security posture. One of my proudest achievements was leading a team in the successful implementation of a new intrusion detection system, resulting in a significant reduction in security breaches.
My technical skills include proficiency in network security, penetration testing, and incident response, as well as familiarity with a range of security tools and technologies. I am also adept at communicating complex technical concepts to non-technical stakeholders, facilitating collaboration across departments to ensure comprehensive security measures are implemented.
I am particularly drawn to CyberDefense Solutions because of its reputation for innovation and commitment to excellence in information security. I am enthusiastic about the prospect of actively participating in furthering your company's mission of protecting valuable assets and maintaining the trust of your clients.
Thank you for considering my application. I am eager to further discuss how my skills and experiences align with the needs of your team. Please find my resume attached for your review. I look forward to the possibility of contributing to the success of CyberDefense Solutions.
Sincerely,
Darren Honey
This is a good example of a cover letter because it effectively communicates the candidate's relevant experience and skills in information security. Additionally, it's tailored specifically to the company and position they're applying for.
The letter demonstrates a clear understanding of the company's needs and showcases the applicant's enthusiasm for contributing to its mission.
Bad information security analyst cover letter example:
Hi there,
I want to be the Information Security Analyst at your company. I'm confident that my 2 years of experience in computer programming make me suitable for the job. I'm great with computers and know all the latest software programs. So I'm sure I can handle any challenge that will come up. Let me know if you need any additional info from me - thanks!
See ya,
Jordan
This is a bad example since it doesn't mention relevant qualifications or experience that the candidate has. It also fails to highlight why the job-seeker is suitable for the position or how the organization could benefit from hiring them.
In addition, the language used is very informal, which is inappropriate for professional communication.
Cover letter for an entry-level information security analyst:
Dear Mr. Stephens,
I am writing to express my interest in the entry-level information security analyst position at SilverTech Innovations, as advertised on your company's career page. As a recent graduate with a degree in Cybersecurity and a strong passion for protecting digital assets, I am eager to contribute my skills and learn from experienced professionals in the field.
During my academic studies, I gained foundational knowledge in areas such as network security, cryptography, and risk assessment. I completed coursework and hands-on projects that equipped me with the technical skills necessary to analyze security threats, implement protective measures, and respond to incidents effectively.
Additionally, my internship experience at SecureTech Solutions provided me with practical exposure to real-world security challenges and reinforced my commitment to pursuing a career in information security.
I am particularly drawn to SilverTech Innovations because of its forward-thinking approach to cybersecurity solutions. I am impressed by your dedication to staying ahead of emerging threats and leveraging cutting-edge technologies to protect sensitive information. I am excited about the opportunity to contribute to your team and further develop my skills under your mentorship.
Thank you for considering my application. I am eager to bring my enthusiasm, dedication, and willingness to learn to the information security team at SilverTech Innovations.
Please find my resume attached for your review. I am available at your earliest convenience for an interview and look forward to the possibility of discussing how I can contribute to the success of SilverTech Innovations.
Sincerely,
Juan Giffin
This cover letter effectively showcases the candidate's enthusiasm and readiness to contribute to the information security field, despite being an entry-level applicant.
It highlights relevant academic and internship experiences, aligning them with the company's goals and demonstrating a genuine interest in joining their team.
Create your professional Cover letter in 10 minutes for FREE
Build My Cover Letter
Proofreading
It is vital to reread and spellcheck your information security analyst resume and cover letter. Well-written application materials can cause the difference between getting an interview and not.
To ensure your documents are error-free, here are tips to follow:
- Take the time to read through the papers multiple times or have someone else review them.
- Use a basic spelling and grammar checker. Numerous services can help identify any errors you may have missed.
- Reading aloud helps catch mistakes that might not appear on paper.
Proofreading resumes and cover letters is crucial to ensure professionalism and accuracy, as errors can detract from the overall impression.
Create your professional Resume in 10 minutes for FREE
Build My Resume
Conclusion
In conclusion, writing an effective information security analyst resume requires a strategic approach. By emphasizing relevant skills, experiences, and certifications, you can showcase your qualifications to potential employers in the best light.
With the help of our writing guide and by employing the online resume AI builder, you will create a document that not only highlights your expertise but also positions you as a strong candidate in the competitive field of information security analysis.